More compact and dependable security measures

We do not stop at implementation, but cover everything from day-to-day operations to incident response. We provide security measures that truly work onsite and can be trusted for a long time.
AI x experience optimized speedy security measures
-
Advanced security response by AI
AI visualizes unknown attacks that cannot be captured by rule-based systems through anomaly detection and behavior analysis.
Real-time analysis of huge logs, prioritization and automatic response speeds up the process from detection to recovery. -

On-site capabilities backed by 63 years of experience
For over 60 years, we have supported a wide variety of industries with a focus on the financial industry.
As an independent SI with a thorough understanding of business flow, we provide consistent support from implementation to operation and maintenance. We provide effective countermeasures based on on-site sensory values.
AI measures are a given. Why do we need experience now?
AI is a powerful tool, though, but there are certainly areas of decision making that cannot be left to are areas of decision-making that cannot be left to AI. However, there are certain areas of decision-making that cannot be entrusted to AI.
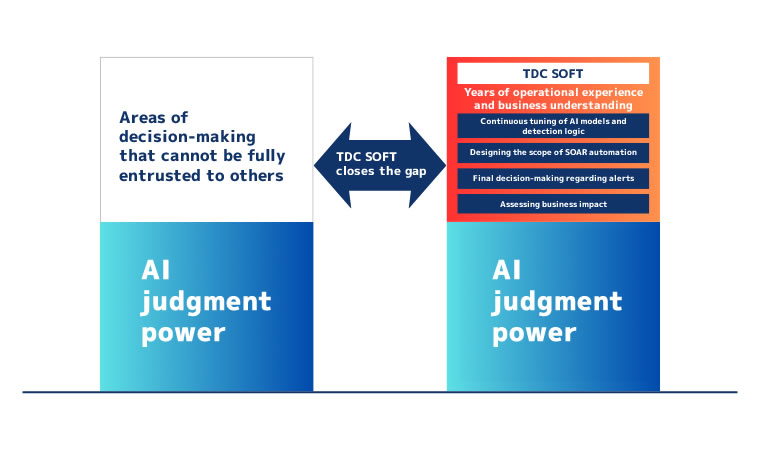
Continuous tuning of AI models and detection logic
Continuous adjustment of detection accuracy is essential to keep up with new attacks, increase or decrease false positives, and take into account changes in departmental operations.
Experience is required to understand the site situation and tune in appropriately.
Final decision on alerts
There are situations where it is difficult to judge by AI alone, such as cases where there is a possibility of legitimate business even with suspicious communications, or a change in behavior immediately after the introduction of a new system.
Human judgment based on business understanding prevents erroneous responses.
Design of SOAR automation scope
While an automated response is effective, unconditional blocking can lead to a halt of the entire operation.
Depending on the nature of the incident, it is important to design how much to automate and where to interject human verification.
Determining Business Impact
The impact of a system outage on operations and customers differs for each industry and business. In order to balance security and business continuity, it is essential to make realistic decisions based on the degree of impact.
Security of TDC Soft

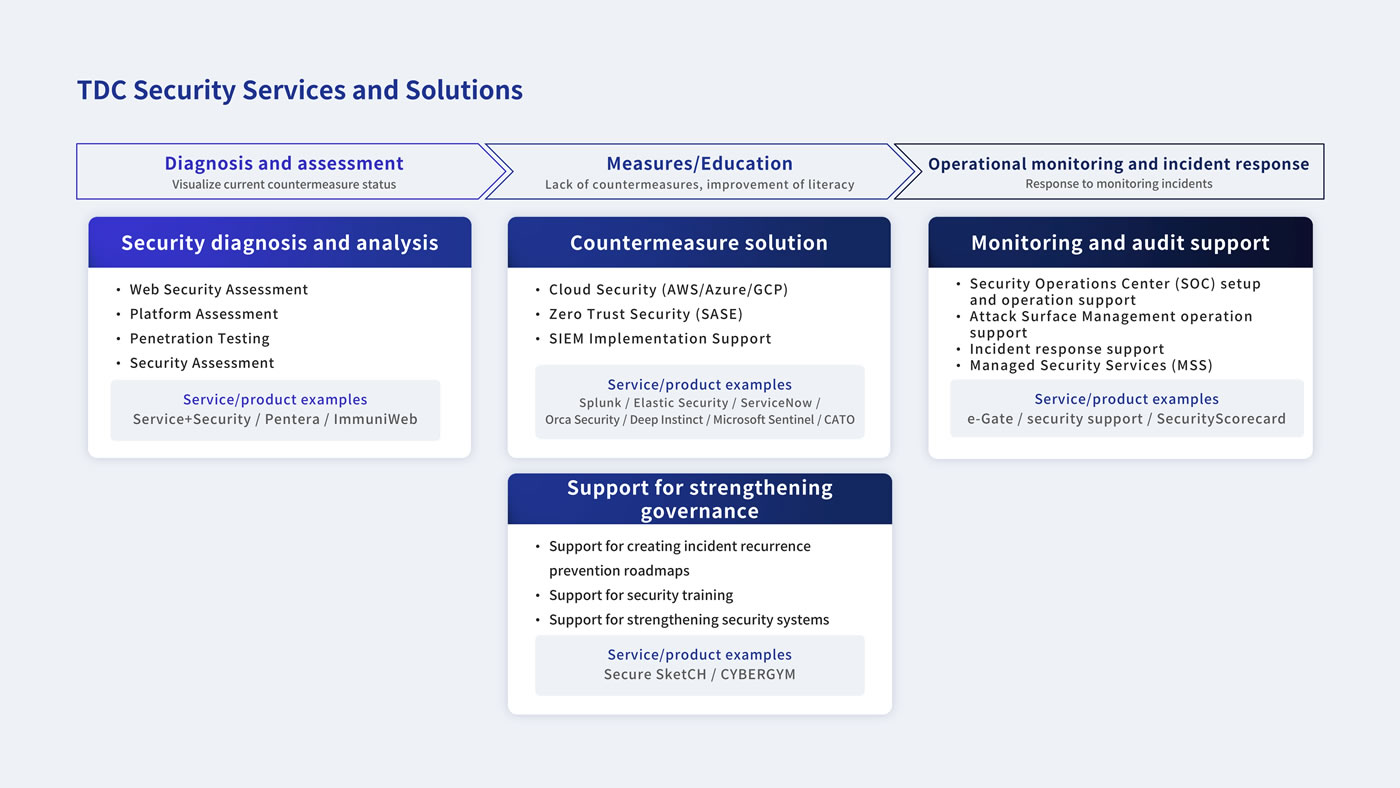
Overall picture of security measures
(1) Diagnosis and Assessment
Organize and visualize the current system configuration, business operations, and assets to be protected.
Clarify risks and priorities, and create a foundation for security measures without excesses or deficiencies.
② Countermeasures and education
Design and implement security measures suitable for the environment and business.
We design and implement security measures that are appropriate for the environment and operations, including the latest architectures such as Zero Trust, and educate users with an eye on operations.
3) Operation monitoring and incident response
Continuous support from log monitoring and alert analysis to incident response.
Combines AI utilization and human judgment to achieve quick and realistic response.
Points to keep in mind
Creating a mechanism, not simply introducing a product
We do not simply introduce a product, but design a security “mechanism” that fits the customer’s needs, taking into account cost, assets to be protected, and operational structure.
Overall optimization including network
We utilize our knowledge of both security and networking to achieve secure and effortless connections while looking at the entire system, both internally and externally.
The peace of mind that only TDC Soft can provide
Preventing problems such as “the introduction of AI but not its operation” through our design and know-how that extends to post-introduction operations. Appropriate use of AI based on an understanding of its characteristics, maximum effect at minimum cost Threats are visualized, and the situation is understood. Threats are visualized, making it easy to grasp the situation. Early detection and prompt response are made possible through log monitoring and AI analysis, and a stable operation system can be built by eliminating the need for personnel by maintaining and automating procedures. Furthermore, through assessments, assets that really need to be protected are clarified.
Concept of Service Provision
TDC Soft’s security services are, TDC Software’s security services are provided from the customer’s issues to design, construction, and operation. TDC Soft’s security services are focused on providing a comprehensive service from design to construction and operation, starting from the customer’s issues.
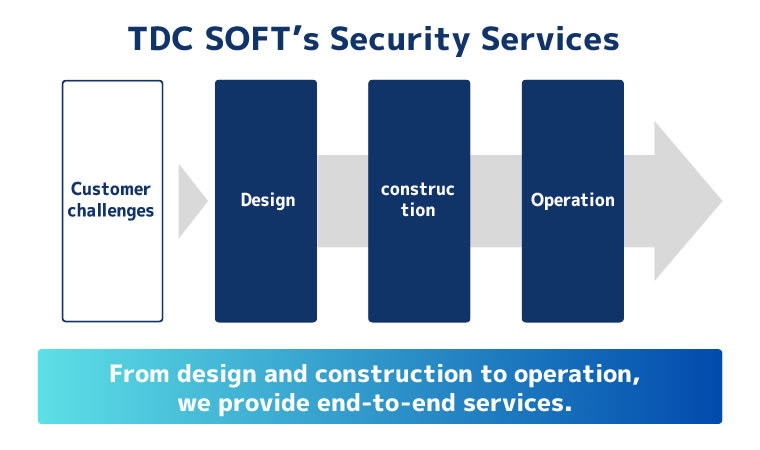
Hearing and organization of issues
We carefully listen to the concerns and anxieties that the field has, as well as the actual status of daily operations. We go beyond mere confirmation of requests to clarify the background and essence of the issues while sorting out the current system configuration, operation system, past troubles and concerns. Based on the assets to be protected and the degree of impact on business operations, we determine the priority points to be addressed and design realistic security measures without excesses or deficiencies.
Integrated support from design, construction, to operation
We provide comprehensive support from network construction, selection and implementation of security products, to post-implementation operation and maintenance. We design a configuration suitable for your business and operation system, not a specific product. We are particularly strong in building security infrastructures based on the premise of operation, including zero-trust, and we can establish a system that can be operated stably after implementation. We realize security with continuity that can respond to changes in the environment and organizational growth.
consulting
We support not only technology, but also organization, business, and operation systems. We aim to ensure that security measures function without difficulty in the field.
Zero Trust Implementation Services
What is Zero Trust?
No dependence on internal or external boundaries, The concept is to continue operations safely based on the premise that people, devices, and access conditions are constantly verified. The concept is not to prevent intrusion completely, but to ensure that business operations can continue safely. It is not about preventing intrusion completely, minimize damage and keep the business running. minimize the damage and keep the business running.
Phase 1: Zero-trust of network and terminals
Implementation of a secure and flexible access infrastructure
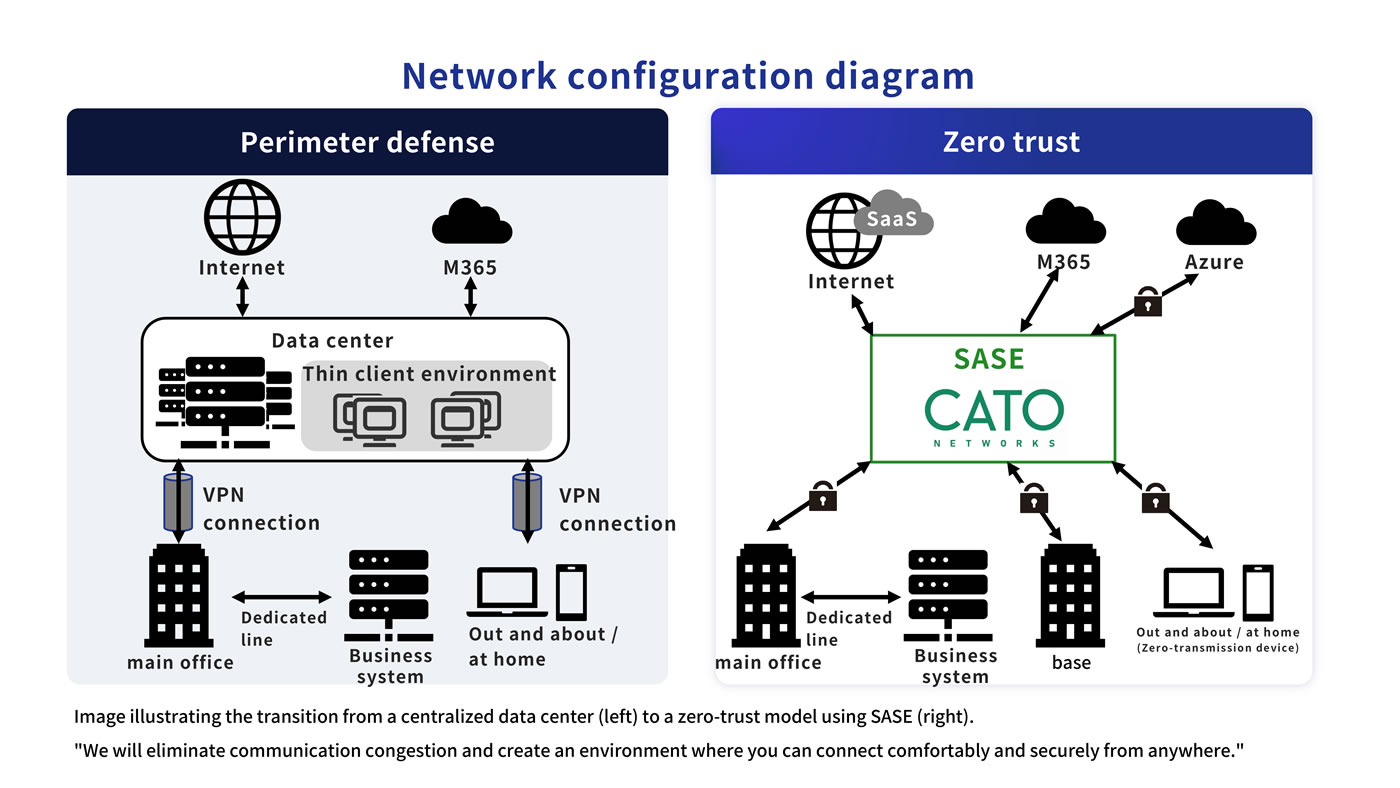
SASE (CATO) eliminates VPN instability and creates a comfortable and secure cloud connection environment that does not go through data centers.
Implementation of Zero Trust PC Infrastructure
Transition to cloud management by Microsoft Intune to realize a terminal environment where the latest security policy is always applied regardless of location.
Phase 2: Advanced data protection and operational monitoring
Advanced Authorization and Information Control
Optimize functions of Microsoft 365 E5, etc., and implement anti-spoofing and control of unauthorized removal of critical data (DLP) in line with actual business operations.
Enhancement of incident response capabilities
Combine EDR and operation logs (SKYSEA, etc.) to establish a system that can visualize and detect risks from both cyber attacks and internal fraud.
Free videos of seminar lectures are now available.
A video of the “Real-life record: ‘Pitfalls’ and ‘Overcoming’ the ‘Pitfalls’ of Introducing Zero Trust,” which was presented at the “Cyber Security Measures in the Zero Trust Era 2026 Winter” hosted by SB Creative in January 2026, is now available on YouTube.
Zero Trust is not “just install the product and be done with it. In this video, we focus on “what really happens in the field,” which does not appear even if you search for it. We hope you will find it useful in considering and promoting the introduction of Zero Trust.
Case Studies
-

Kirabo Life Design Securities, Zero Trust Construction (CATO)
In response to issues such as unstable VPN connections and complicated password management, a zero-trust environment centered on Cato SASE Cloud was introduced. While ensuring a high level of security in accordance with financial standards, the convenience and operational efficiency were greatly improved in a short period of time of only 3 months.
-

Energy Industry Incident Response Procedure Development
Standardized decision-making criteria and procedures in order to break away from incident response that depends on the person in charge. Clarified the response flow in the event of an incident, and created a system that allows anyone to respond consistently up to consensus building with the management and executive levels.
-

Energy Industry SIEM Environment Replacement
To improve detection accuracy while reducing operational costs, we reviewed the existing SIEM environment, migrated the SIEM infrastructure to Elastic Cloud, and supported rule redesign to achieve an efficient and easy-to-operate system.


